What is a Denial-of-Service (DoS) Attack?
A cyberattack is an illegal attempt to break into a computer system or network. The goal is often to steal, change, or destroy sensitive data. Some attacks aim to block access or demand money from users. One common type of cyberattack is the DoS attack (Denial-of-Service). In this attack, hackers overload a system with traffic, making it slow or completely unavailable.
What is a DoS attack?
A denial-of-service (DoS) attack overloads a machine or network to render it inoperable. Attackers accomplish this by sending more traffic than the target can handle, causing it to fail and rendering it unable to serve its regular users. Email, online banking, websites, and any other service that relies on a targeted network or computer are examples of targets.
Unlike a virus and worm or malware, A DoS attack does not require the execution of a specific program. Instead, it takes advantage of a flaw in how computer networks communicate.
What is the main goal of a DoS attack?
A DoS attack attempts to disrupt the availability of web applications. Unlike other types of attacks, A DoS attack is designed to slow or shut down a website rather than steal information.
Best-suited Ethical Hacking courses for you
Learn Ethical Hacking with these high-rated online courses
Famous DoS attacks
Here are some of the famous DoS attacks:
- The Microsoft attack: Microsoft mitigated the most significant DDoS attack recorded in November 2021, attacking an Azure client with a throughput of 3.45 Tbps and a packet rate of 340 million PPS. In addition, the use of DDoS to demand ransom payments for stopping attacks — or not launching them in the first place — increased in 2021.
- The Google attack: Google’s Security Reliability Engineering team measured a record-breaking UDP amplification attack originating from several Chinese ISPs (ASNs 4134, 4837, 58453, and 9394) in 2020 which remains the largest bandwidth attack that Google is aware of.
- The AWS attack: Amazon’s AWS Shield service was credited with mitigating the largest DDoS attack ever recorded, a 2.3 Tbps attack in mid-February 2020. The incident was revealed in the company’s AWS Shield Threat Landscape [PDF], a report detailing web attacks mitigated by Amazon’s AWS Shield protection service.
Must Explore- What is a Phishing attack?

What are the different types of Dos attacks?
There are several kinds of denial-of-service attacks:
Resource exhaustion
Resource exhaustion attacks are computer security exploits that cause the targeted program or system to crash, hang, or otherwise interfere. They are a type of denial-of-service attack, but they differ from distributed denial-of-service attacks, which involve flooding a network host with requests from multiple locations.
Resource exhaustion attacks cause the targeted infrastructure to consume all of its available memory or storage resources, slowing or stopping the service entirely.
Flood attack
In a flood attack, attackers send a large volume of traffic to a system, preventing it from inspecting and allowing permitted network traffic. An ICMP flood attack, for example, occurs when a system receives an excessive number of ICMP ping commands and has to use all of its resources to respond.
Flood attacks send an enormous number of packets that overwhelm server capacity. The Firebox can defend against various types of flood attacks, such as IPSec, IKE, ICMP, SYN, and UDP.
Crash attack
Crash attacks seek to altogether disable the monitor by causing it to fail or run out of resources. Like the overload attack, the crash attack has two phases: the first in which the attacker crashes the monitor, and the second in which they proceed with an intrusion.
Crash attacks are less common when cybercriminals send bugs that exploit flaws in the targeted system, causing the system to crash. Crash and flooding attacks make it impossible for legitimate users to access online services such as websites, gaming sites, email, and bank accounts.
Distributed denial-of-service (DDoS) attack
A distributed denial-of-service (DDoS) attack is a type of DoS attack in which the traffic used to overwhelm the target is spread across multiple sources. When an attacker exploits this method of attack, you cannot stop the attack simply by blocking the source of traffic.
This type of attack exploits the specific capacity limits that apply to any network resource, such as a company’s infrastructure that supports its website. During this attack, an attacker will send multiple requests to the attacked web resource in order to exceed the website’s capacity to handle various requests. Thus, preventing it from functioning correctly.
DDoS attacks commonly target the following targets:
- Websites for online shopping
- Online gambling establishments (Online Casinos)
- Any company or organization that relies on online services
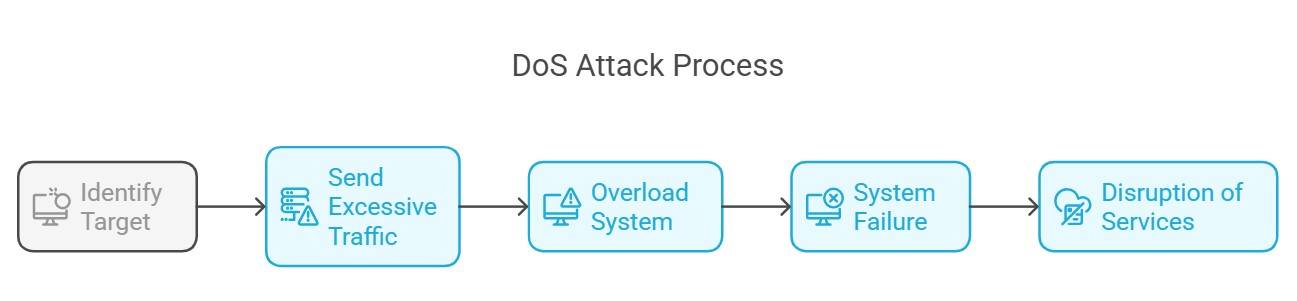
How do DoS attacks work?
Denial-of-service attacks typically target high-profile organizations’ web servers, such as banking, e-commerce, media companies, and government entities. Perpetrators target organizations’ assets in one of two ways: by flooding their networks with large amounts of traffic or sending malicious data such as bugs that cause a crash.
Whatever method an attacker uses, the goal is to bring the network or machine down. If the DoS victim is, for example, an internet or cloud service provider for others, additional networks or assets that the DoS attackers did not specifically target may also be impacted.
Let’s take an example to understand the working of DoS attacks in a much better way. Assume you want to order food from an e-commerce site. Your computer sends a small data packet to the website. The packet functions as a “hello.” In essence, your computer says, “Hello. I want to visit you. Please allow me to enter.”
When the server receives your computer’s message, it responds with a brief statement that essentially says, “OK.” “Are you for real?” “Yes!” says your computer and communication are established. The website’s homepage then appears on your screen, and you can explore it. As you click restaurants, place orders, and conduct other transactions, your computer and the server continue to communicate.
What tools are commonly used to execute DoS attacks?
Some of the common tools used to execute DoS attacks are:
- LOIC (Low Orbit Ion Cannon): An open-source tool that enables users to perform stress tests on servers by flooding them with TCP, UDP, or HTTP requests.
- HOIC (High Orbit Ion Cannon): Similar to LOIC, but more powerful. It can attack multiple targets and allows the use of customizable scripts.
- Smurf Attack Tools: These tools exploit network vulnerabilities by sending ICMP requests to amplifiers, which then flood the target with traffic.
- RUDY (R-U-Dead-Yet?): A web application stress testing tool that simulates a large number of users accessing and overwhelming web applications.
- Botnets: Networks of compromised computers can be directed to perform large-scale coordinated attacks, often controlled via a command-and-control server.
- Slowloris: This tool enables attackers to hold connections open on a web server while sending partial HTTP requests, leading to resource exhaustion.
- Ping of Death: This tool sends malformed or oversized packets to crash target systems that are vulnerable to this type of attack.
DDoS vs. DoS attacks
Let’s try to understand the difference between DDoS and DoS using a tabular format:
| DDoS | DoS |
|---|---|
| In a DDoS attack, multiple systems target the victim’s system. | Only a single system targets the victim’s system in a DoS attack. |
| Victim PC is loaded from the data packet sent from multiple locations. | Victim PC is loaded from the data packet sent from a single location. |
| DDoS attacks are more rapid than DoS attacks. | DoS attacks are slower than DDoS attacks. |
| DDoS attacks are difficult to track down. | DoS attacks are simple to track down. |
| DDoS attacks enable an attacker to flood the victim network with massive amounts of traffic. | DoS attacks have less traffic volume than DDoS attacks. |
The primary distinction between DoS and DDoS attacks is that DDoS attacks use multiple internet connections to knock the victim’s computer network offline, whereas DoS attacks use a single connection. To learn in-depth, read the Difference Between DOS and DDOS Attack article.
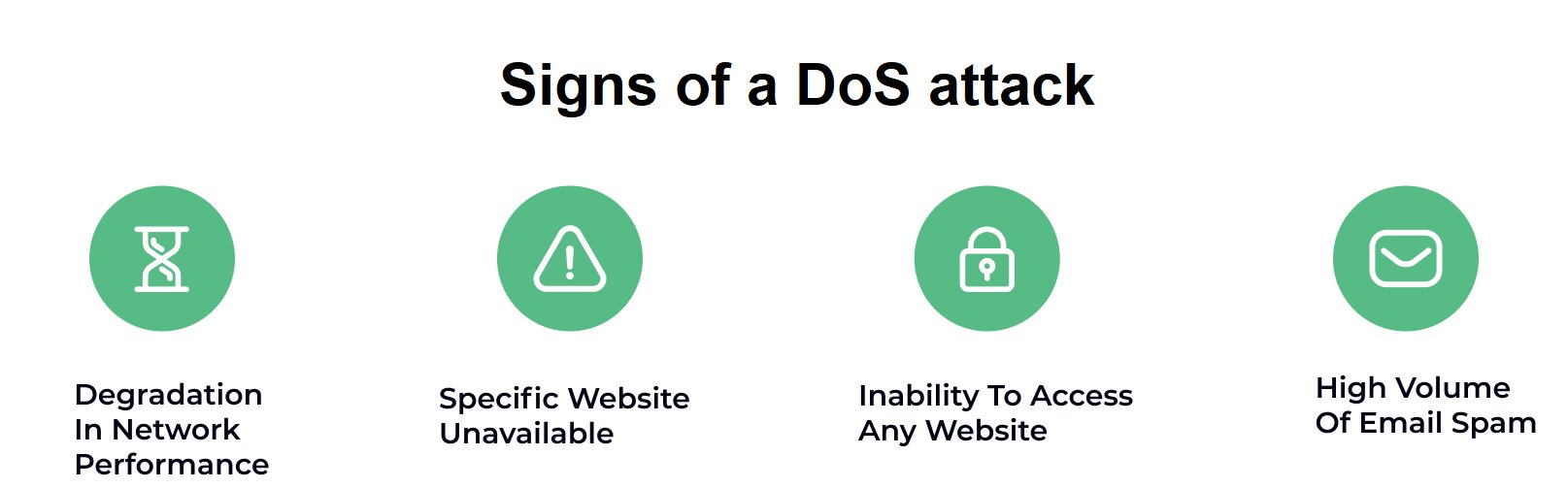
How might you tell when a computer is under a DoS attack?
While distinguishing an attack from other network connectivity errors or high bandwidth consumption can be problematic. But, for clarity and ease, you can look for some of these characteristics that may indicate an attack is underway.
The following are signs of a DoS attack:
- Unusual slow network performance, such as long file or website load times
- Inability to load a specific website, such as your web property
- An unexpected loss of connectivity among devices on the same network
- A high volume of email spam.
What are the common motivations behind DoS attacks?
Common motivations behind DoS attacks include:
- Political Activism: Hacktivists may attack to promote a cause or protest against an organization or government.
- Financial Gain: Attackers may demand ransom to stop the attack or may disrupt competitors to gain market advantage.
- Revenge: Former employees or disgruntled individuals might launch attacks out of frustration or anger.
- Distraction for Other Attacks: A DoS attack can divert attention while a more serious breach occurs elsewhere.
- Testing Skills: Some attackers might launch DoS attacks simply to demonstrate their skills or challenge themselves.
- Botnet Recruitment: Attackers may use DoS attacks to test and strengthen their networks of compromised devices (botnets).
- Thrill or Fun: Some individuals may attack for the thrill or as a form of entertainment, viewing it as a game.
- Corporate Espionage: Competing businesses might engage in DoS attacks to disrupt rivals temporarily.
How to prevent DoS attacks?
Organizations can take the following steps to protect against and prevent denial-of-service attacks:
Analyze network traffic: Network traffic can be monitored and analyzed using a firewall or intrusion detection system. Administrators can configure rules to generate alerts for unusual traffic, identify traffic sources, or drop network packets that meet specific criteria.
Create and practice a DoS attack response plan: The key is to create and practice a DoS attack disaster recovery plan covering communication, mitigation, and recovery.
Improve your security posture: This includes hardening all internet-facing devices to prevent compromise, installing and maintaining antivirus software, establishing firewalls configured to protect against DoS attacks, and employing robust security practices to monitor and manage unwanted traffic.
Reduce attack surface area: One of the best ways to mitigate DDoS attacks is to reduce the surface area that an attacker can attack, limiting attacker options and allowing you to build protections in a single location.
Monitor traffic: Businesses can sign up for a service that detects and redirects abnormal traffic flows associated with a DoS attack while allowing regular traffic to flow through the network.
Deploy Firewalls: A good practice is using a Web Application Firewall (WAF) to protect against attacks such as SQL injection or cross-site request forgery that attempt to exploit a vulnerability in your application.
Recently completed any professional courses/certifications from the market? Tell us what you liked or disliked in the course for more curated content.
FAQs
What is a Denial of Service (DoS) attack?
A DoS attack aims to make a service unavailable to users. Attackers flood a server with excessive requests, overwhelming it and causing it to crash or slow down.
How does a denial of service occur?
The best way to detect and identify a DoS attack is to monitor and analyze network traffic.
What can you do to prevent DoS attacks?
There are numerous ways to prevent a DDoS attack, such as developing a Denial of Service Response plan, strengthening your network, practicing good cyber hygiene, utilizing anti-DDoS hardware and software, migrating to the cloud, etc.
What industries are the most vulnerable to DoS attacks?
DoS attacks frequently target high-profile organizations' web servers, such as banks, commerce, media companies, and government and trade organizations.
What is the primary purpose of a DoS attack?
A DoS attack, unlike other types of attacks, is intended to slow or shut down a website rather than steal information.
How does a DoS attack work?
Attackers send a massive amount of traffic to a target server. This enormous amount of data overwhelms the server's resources, making it unable to respond to legitimate requests.
What are the types of DoS attacks?
There are several types, such as Volume-based attacks, Protocol attacks, and Application layer attacks. Each type targets different aspects of the network or server.
What is a Distributed Denial of Service (DDoS) attack?
A DDoS attack is a more severe version of a DoS attack. It uses multiple compromised computers to flood a target, making it harder to defend against.
What are the effects of a DoS attack?
DoS attacks can cause significant downtime, revenue loss, and reputation damage. They can also lead to increased recovery costs and customer dissatisfaction.
How can organizations protect against DoS attacks?
Organizations can use firewalls, intrusion detection systems, and rate limiting. Regular updates and security audits also help strengthen defences.
Are DoS attacks illegal?
Yes, DoS attacks are illegal in many countries. They violate laws related to computer security and can lead to severe penalties for the attackers.
How can one report a DoS attack?
If you suspect a DoS attack, report it to your internet service provider (ISP) and local authorities. They can help investigate and mitigate the attack.