Top 65 Linux Interview Questions and Answers (2023)
This article covers the 65 most asked Linux interview questions that will help you in improving your technical knowledge on Linux.
Linux is one of the best-known and widely-used operating systems. It is very popular among IT companies of all shapes, sizes, and functions because of its security, portability, scalability, and configuration options. There is a huge demand for Linux professionals in India and worldwide. Companies are willing to offer lucrative salaries to Linux professionals. This article lists 50+ frequently-asked Linux interview questions to help you excel in your next job interview.
Check out free Linux courses.
Top Interview Questions on Linux for experienced
Here are the top 50+ Linux questions and answers covering the basic and advanced Linux concepts to help freshers and aspiring Linux professionals prepare for their interviews. This list also covers some commonly asked Linux interview questions for experienced professionals to boost your interview preparation.
Explore Online Linux Courses
Q1. What operating system is Linux based on?
Ans. Linux is based on Unix operating system. It is a family of multi-user and multitasking operating systems developed in the 1960s and 1970s by AT&T Bell Labs. Linus Torvalds created Linux in 1991 as a free and open-source operating system based on the Unix philosophy. However, Linux is not a direct copy of Unix and has been developed independently with unique features and designs.
Also, Explore:
| Top Web Development Courses | Popular Big Data Courses |
| Top Programming Courses | Popular QA and Testing Courses |
Q2. What is the difference between Unix and Linux?
Ans. Many people think that Unix and Linux as synonyms. But Linux is the clone of Unix. Some of Linux’s features are similar to Unix, yet they have some key differences. The major differences between Linux and Unix are:
| Unix | Linux |
| Unix is an operating system used in Intel, HP, internet servers, and more. | It is an operating system used for computer hardware & software, game development, and more. |
| Different versions of UNIX have different cost structures. | It has both free distributions and paid versions are available. |
| It is mainly used in mainframes, internet servers, and workstations. | It can be used by anyone including home users, developers, etc. |
| The file support system includes jfs, gpfs, hfs, ufs, vxfs. | The file support system includes Ext2, Ext3, Ext4, Jfs, ReiserFS, Xfs, Btrfs, FAT, NTFS. |
| The common desktop environment serves as a GUI. | It offers two GUIs: KDE and Gnome. |
| It is also highly secured and has around 85-120 viruses listed to date. | Offers higher security. It has around 60-100 viruses listed to date. |
| Examples: Solaris, OS X, All Linux. | Examples: Red Hat, Fedora, Kali Linux, Debian, Android, Ubuntu. |
Also, explore Linux vs. Windows
Q3. Is it legal to edit the Linux kernel?
Ans. Yes, as it is under General Public License (GPL), and anyone can edit.
Also Read: Learn Basic Linux Commands (With Syntax)
Q4. What are the basic components of Linux?
Ans. This is one of the popularly asked interview questions on Linux. The Linux operating system consists of the following three components:
1. Kernel: It is the core part of Linux and is responsible for all major operating system activities. Linux Kernel is free and open-source software that manages user hardware resources. It consists of various modules and interacts directly with the underlying hardware. Kernels prevent conflicts between different processes. Different types of the kernel are:
- Monolithic kernels
- Exo kernels
- Hybrid kernels
- Micro kernels
2. System Library: System libraries are special functions using which application programs access Kernel’s features. System libraries are responsible for implementing most of the operating system’s functionalities. They do not require kernel module’s code access rights.
3. System Utility: These programs perform specialized, individual-level tasks.
Explore the popular Operating System Courses
Q5. What is LILO?
Ans. LILO stands for Linux Loader, a bootloader program used on some Linux distributions to load the operating system into memory when the computer starts up.
The LILO bootloader works by accessing the Master Boot Record (MBR) of the hard drive and loading the necessary files to start the Linux kernel. LILO can also be configured to allow the user to choose between different operating systems installed on the same machine at boot time.
Q6. Which command would you use to remove the password assigned to a group?
Ans. The gpasswd – r removes the password assigned to a group.
Q7. What is BASH?
Ans. BASH stands for Bourne-Again SHell and is a Unix shell, which is a command-line interface for interacting with an operating system. It is the default shell on most Linux distributions and macOS.
BASH provides a wide range of features, including command history, tab completion, shell scripting, and job control. It allows users to execute commands and scripts, manipulate files and directories, and perform system administration tasks.
Q8. What is the difference between BASH and DOS?
Ans. This is one of the most commonly asked Linux interview questions.
There are three key differences between BASH and DOS:
- BASH commands are case sensitive while DOS commands are not
- BASH follows no convention in naming files, while DOS follows a convention
- Under BASH, / character serves as a directory separator while in DOS \ serves as the directory separator.
Q9. What is the alternative method for a GUI installation in Linux?
Ans. Linux provides textbase installation as the alternative method of GUI installation.
Q10. What is the root account in Linux?
Ans. The root account is like a systems administrator account and allows full control of the system.
Q11. How can you find out how much memory Linux is using?
Ans. Use the “concatenate” command from a command shell: cat /proc/meminfo for memory usage information.
Q12. Does the Ctrl+Alt+Del key combination work on Linux?
Ans. Yes
Q13. How do you create a new user without logging on as a root user?
Ans. Using the su command.
Q14. What is the minimum number of partitions that you need to install Linux?
Ans. Minimum two partitions are needed for installing Linux.
Q15. Which command would you use to create a file system on a new hard drive?
Ans. The mkfs command
Q16. Which command is used to review boot messages?
Ans. The dmesg command is used for reviewing boot messages.
Check out the best Linux Courses
Q17. Which file is used to automatically mount file systems?
Ans. Fstab file will automatically mount file systems.
Q18. What is the difference between internal and external commands?
Ans. Internal commands are those that are already loaded in the system. External commands are those which can be executed at any time and are independent.
Q19. What is the difference between the home directory and the working directory?
Ans. The home directory is the default working directory when a user logs in.
The working directory is the user’s current directory.
Q20. Which daemon controls the print spooling process?
Ans. The line printing daemon
Also explore:
- Paid and free online courses by Coursera
- Popular online Udemy courses
- Top online edX courses
Q21. How can you check the memory status?
Ans. free -m to display output in MegaByte
Q22. Explain how to uninstall the libraries in Linux?
Ans. By using the command, sudo apt-get remove library_name
Q23. Which command is used to delete a group?
Ans. The groupdel command deletes a group.
Q24. How do you terminate an ongoing process?
Ans. Use the kill command followed by the pid in order to terminate that process. To terminate all processes at once, use kill 0.
Q25. Can Linux computers be made a router so that several machines may share a single Internet connection? How?
Ans. Yes, by IP masquerading, you can turn a Linux computer into a router.
Q26. What daemon is used for scheduling of the commands?
Ans. The crontab command is used for the scheduling of commands.
Check out the best Online Emerging Technologies Courses
Q27. Name the different modes used with vi editor?
Ans. There are two modes in the vi editor:
Command Mode: This is the default mode in which the vi editor opens. In this mode, users can issue commands to navigate the document, perform editing tasks, and save or quit the file. In command mode, the vi editor does not display any text that is being typed.
Insert Mode: It inserts new text into the document. To enter Insert mode, the user can press the “i” key or any other key combination that switches from Command mode to Insert mode. In Insert mode, the vi editor displays any text that is being typed.
Other modes can be accessed from Command mode:
Visual Mode: It is used to select text in the document. In Visual mode, the user can select text using various commands and then perform editing tasks on the selected text.
Replace Mode: This replaces existing text with new text. In Replace mode, the vi editor replaces existing characters with new characters as the user types.
Ex Mode: It executes commands that are not available in Command mode. To enter Ex mode, the user can type a colon (:) in Command mode and then type the Ex command they want to execute. Ex commands are used to save, quit, or search the document, among other tasks.
Q28. What are File Permission groups in Linux?
Ans: Following are three user based permission groups for each file and directory:
- Owner
- Group
- All Users
Q29. Name the different types of file systems in Linux.
Ans: There are different types of file systems in Linux:
- Ext
- Ext2
- Ext3
- Ext4
- JFS
- XFS
- Btrfs
- Ufs
- Autofs
- Devpts
- Ntfs
- swap
Q30. What is the procedure to set the umask permanently for a user?
Ans: If the umask command is used without any arguments, it will display the current mask. Ocotal representation and Symbolic representation. are two types to set the umask permanently.
Q 31. Why do we use /etc/resolv.conf and /etc/hosts files?
Ans. /etc/resolv.conf files contain the nameserver details and are used for configuring the DNS name servers. /etc/hosts files translate and map hostnames/domain names to the relevant IP address.
Q32. What is the procedure to convert the default run level in Linux?
Ans: We can use the init command to convert the default run level in Linux.
Explore the Most In-Demand Tech Skills
Q33. How to share a directory with the help of nfs?
Ans: To share a directory with the help of NFS, we have to edit the configuration file, ‘/etc/exports’, and add an entry like directory name ‘/’. Then, restart the NFS service.
Q34. How can we lock the user account in Linux?
Ans: We can lock user account for the security of users so that unauthorized users cannot log in. There are a few ways to lock the user account:
- Disable the password with the help of passwd command.
- Delete the user account with the help of usermod command or change command.
- Switching the shell using nologin command ( /sbin/nologin ).
Q35. Explain the grep command in Linux?
Ans: grep command is used to the global search for regular expressions.
Syntax:
grep [options] pattern [files]
Q36. What is the role of the cp command in Linux?
Ans: cp command in Linux is used to copy files and directories. We can also use it for the backup of files or directories.
Syntax: $ cp file name
Q37. How to delete a directory in Linux?
Ans: The rmdir and rm commands are used to remove a directory in Linux.
rmdir command deletes the empty directory.
Syntax:
rmdir [-p] [-v | –verbose] [–ignore-fail-on-non-empty] directories
rm command deletes non-empty directories and their contents.
Syntax:
rm -rf dir-name
rm -rf /path/to/dir/name
Explore the Top Highest Paying IT Certifications
Q38. Mention some Linux file content commands.
Ans: Following are some file content commands:
- head: Display the top lines of the file.
- tail: Display the last lines of the file.
- cat: Concatenate more than two files.
- more: Display the content in pager form to view in the terminal.
Q39. Explain what PIPE in Linux is?
Ans: A pipe is a form of redirection in Linux, it is mainly used to combine two or more two commands, and the output of one command can take as input to the next command.
Syntax:
command_1 | command_2 | command_3 | …. | command_N
Q40. Explain lsof command in Linux?
Ans: lsof command lists the open files assigned to the application. It also lists the processes that opened them.
Q41. Explain the df command in Linux?
Ans: The df (display free disk space) command troubleshoots disk space problems.
df Command Example:
df -h
Q42. Explain what does (cd dir && command) do?
Ans: The cd dir && command moved to the dir and used to execute the command, then returns to the current directory.
Q43. What is the role of pushd command in Linux?
Ans: The pushd command is used to put recent dir on the stack so it can pop back to it.
Q44. What is the role of pwd command?
Ans. The pwd or print working directory command is a commonly used command in Linux. It is used to write the full pathname of the current working directory. It will print the path of the working directory starting from the root.
Q45. What is CLI? What are its advantages and disadvantages?
Ans. This is one of the most important Linux interview questions for experienced candidates. CLI stands for Command Line Interface. It is a non-graphical, text-based interface that enables users to interact with computers. Users can type declarative commands and instruct the computer to perform operations using the Linux interface. It is based on the response transaction process and offers great flexibility.
Advantages of CLI:
- A lot faster and more efficient to use by experts (those who know the commands).
- Offers great flexibility.
- Does not use much CPU processing time.
- Does not require Windows to run.
- Needs fewer resources.
- Needs much less memory (Random Access Memory).
Disadvantages of CLI:
- It can be very confusing for new users.
- It requires a lot of commands to be learned and remembered.
- Commands need to be typed precisely. The command will not respond or fail if there is a spelling mistake.
Now, let’s look at more Linux interview questions and answers for experienced candidates.
Q46. What are symbolic links?
Ans. A symbolic link or symlink in Linux is a file that points to another file or a folder on the computer. It functions like a shortcut in Windows. It lets you instantly access programs, files, or directories without going directly to the entire pathname. Symbolic links are also called ‘soft links’.
Features of Symbolic Links:
- A symbolic link is similar to the file shortcut feature in Windows Operating systems.
- They can be linked across different file systems.
- They contain the path for the original file and not the contents.
Syntax:
ln -s [target file] [Symbolic filename]
- -s – to create a soft (symbolic) link
- [target file] – the name of the existing file for which you are creating the link
- [Symbolic filename] – the name of the symbolic link
Also Read: Top Udemy Courses – Technical Courses for IT Professionals
Q47. How do you change permissions under Linux?
Ans. chmod (change mode) command changes file and directory permissions in Linux. The chmod command consists of at least three parts from the following:
| Access class | Operator | Access Type |
| u (user) | + (add access) | r (read) |
| g (group) | – (remove access) | w (write) |
| o (others) | = (set access) | x (execute) |
| a (all) |
Example:
An owner of a file or directory can change permissions using the following command.
- chmod +rwx filename to add permissions.
- chmod -rwx directoryname to remove permissions.
- chmod +x filename to allow executable permissions.
- chmod -wx filename to take out write and executable permissions.
Also Read: Top Online IT Courses for IT Professionals
Q48. What are the features of Linux?
Ans. This is one of the basic Linux interview questions that you must prepare for your interview.
Following are some of the features of Linux:
- Multitasking: Supports more than one function simultaneously by dividing the CPU time.
- Multiuser capability: Allows multiple users to access the same system resource using different terminals for operation.
- Portable: Linux Kernel and application programs can be installed on any hardware platform.
- Application support: Has its own software repository to download and install applications.
- Security: Provides security in three ways, namely, authentication, authorization, and encryption.
- Hierarchical File System: Provides a standard file structure for arranging system files and user files.
- Open Source: Code is freely available to all.
- Live CD/USB: Provide a live CD/USB so users can run it without installing it.
Q49. What are the different types of Process Management System Calls in Linux?
Ans: Process management uses certain system calls. They are:
| fork () | create a new process |
| exec () | execute a new process |
| wait() | wait until process execution |
| exit() | terminate the process |
| getpid () | to find the unique process id |
| getppid() | to find the parent process id |
| nice () | bias the currently running process property |
Q50. What is Kali Linux?
Ans. Formerly known as BackTrack Linux, Kali Linux is an open-source, Debian-based Linux distribution for penetration testing and security auditing. It was launched in March 2013. It is a rebuild of BackTrack Linux that conforms to Debian development standards. Kali Linux offers various tools for information security tasks such as Penetration Testing, Computer Forensics, and Security Research.
Below are some key features of Kali Linux:
- Accessible
- Multi-platform solution
- Completely free of charge
- Custom Linux Kernel
- Comes with a vast array of penetration-testing tools
- FHS compliant
- Multi-language support
- Customizable
- Can be used on a variety of ARM Devices

Q51. Why is Linux better than Windows?
Linux offers more security and great speed compared to Windows. Windows offers great ease of use, enabling even non-technical people to work on it easily. But it is less secure than Linux as viruses and malware affect windows more quickly. Many corporate organizations prefer Linux as a server and operating system for security.
Q52. What is LinuxShell and how they are used in Linux?
Ans. Some of the commonly used Shells in Linux are:
- Sh: Sh stands for Bourne Shell. This is the original Unix shell and is the ancestor of all other shells. It is a simple shell that does not have many advanced features.
- Bash: It stands for Bourne Again Shell. It is the default for most Linux distributions.
- Ksh: Ksh stands for Korn shell. It is a high-level programming language shell.
- Csh: The C Shell follows C-like syntax. It offers spelling correction and job control.
- Zsh: Z Shell is an interactive shell offering unique features like startup files, login/logout watching, closing comments, and more. It incorporates some features of other Linux shells, such as Bash and Ksh.
- Fish: It stands for Friendly Interactive Shell and provides some unique features like man page completions, web-based configuration, auto-suggestions, and is fully scriptable with clean scripts. It is fully interactive and user-friendly like other shells.
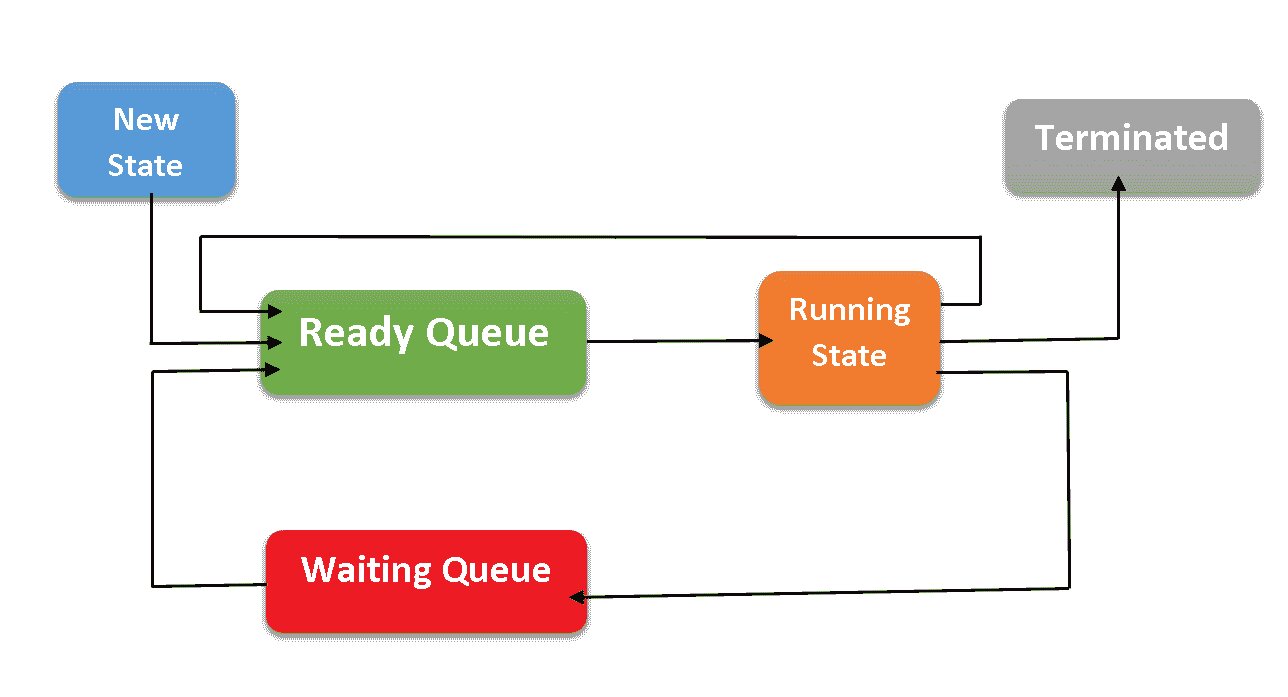
Q53. What are the different process states in Linux?
Ans. This is a popular Linux interview question that you must prepare for.
Linux has the following process states:
- Ready: The process has been created and is ready to run.
- Running: The process is executing and using the CPU at a particular moment.
- Waiting: The process is waiting for an event to occur or for a system resource.
- Terminated/Stopped: A process is usually stopped by receiving a signal.
- Zombie: The process is terminated but still has an entry in the process table.
Q54. What are Daemons in Linux?
Ans. This is another popular Linux interview question. Daemons are programs on Unix-like operating systems that run in the background instead of under a user’s direct control. In Linux, daemons extend the functionality of the base operating system by offering functions that might not be available in the operating system.
A daemon actively listens for a service request and acts upon it simultaneously. On completion of service, the daemon gets disconnected and waits for further requests.
Most have a ‘d’ at the end of the process name. Some of the service daemons for Linux systems are:
- amd – Auto Mount Daemon
- ftpd – FTP Server Daemon
- httpd – Web Server Daemon
- mysql – Database server Daemon
- nfsd – Network File Sharing Daemon
- sshd – Secure Shell Server Daemon
Q55. What is Graphical User Interface?
Ans. Graphical User Interface is a human-computer interface that allows interaction between users and electronic devices through visual indicators and graphical icons. Users can easily interact with the system through these graphical elements or icons. It is visually intuitive and leads to higher productivity. It combines textual and graphical interaction that uses buttons, menus, message boxes, etc.
Q56. What is redirection?
Ans. Redirection refers to the process of directing data from one output to another.
Q57. What is Secure Shell (SSH)? How can we connect to a remote server through Secure Shell?
Ans. Secure Shell (SSH) is a protocol for securely connecting to remote servers and enabling communication between two systems. It is one of the most common methods to access remote Linux servers. It transmits data over encrypted channels leading to high-level security. You will require a domain name and IP address to connect to a remote server through a secure shell (SSH).
Q58. Write the difference between Soft and Hard links.
Ans. Soft Links or Symbolic Links are different types of files that point toward another file. It does not include data in the target file and points towards another entry anywhere within the file system. These links can be used across the file systems. Soft links can be created through the following command:
$ ln -s [original filename] [link name]
Hard Links are a special type of file that point towards the same underlying inode as another file. It can be referred to as an additional name for the existing file on Linux OS. The total number of hard links for a file is displayed through the “ls -l” command. These links cannot be used across file systems and can be created through the following command:
$ ln [original filename] [link name]
Q59. Define swap space?
Ans. Swap space is the substitute space on the hard disk used when RAM or the physical memory is full. The space is used when there is no space left for executing programs.
Q60. What are the benefits of using Network Interface Card (NIC) teaming?
Ans. Load balancing, failover and uptime increase are the major benefits of using NIC teaming.
Q61. What is an inode?
Ans. Inode is the short form of index node. It can be defined as a record in a disk table. In terms of Linux, inodes manage the metadata of the file. Every Linux directory has a file name and an inode number.
The inode number has these attributes.
- Size of the file
- Owner of the file
- Disk Location
- Types of files
- No. of links
- Date and time
- File metadata
Q62. Could you explain what network bonding means and what its types are?
Ans. Network bonding combines more than one network interface to make into a single bonded channel.
There are seven types of network bonding.
- mode=0 (Balance Round Robin)
- mode=1 (Active backup)
- mode=2 (Balance XOR)
- mode=3 (Broadcast)
- mode=4 (802.3ad)
- mode=5 (Balance TLB)
- mode=6 (Balance ALB)
Q63. Name the types of file permissions on Linux.
Ans. Read, write and execute are the three types of file permissions.
Q64. What is the need for LVM on Linux?
Ans. LVM (Logical Volume Manager) is a tool used in Linux systems to manage storage volumes. It allows for easy disk space management by providing features such as logical volume creation, resizing, and migration.
Here are some reasons why LVM is needed on Linux:
Flexible Storage Management: LVM provides a layer of abstraction between the physical disks and the logical volumes, making it easy to manage and manipulate storage space. Logical volumes can be resized, moved, or added easily without changing the underlying physical storage.
Dynamic Storage Allocation: With LVM, physical disks can be added or removed without interrupting the logical volume’s operation, making it easy to expand or shrink storage capacity as needed.
Data Segregation: LVM allows data to be segmented across multiple physical disks or arrays, improving performance and providing redundancy in case of disk failure.
Snapshot Creation: LVM allows for the creation of instant snapshots of logical volumes. These snapshots can be used for backups or testing purposes without disrupting the logical volume.
Easy Migration: LVM makes it easy to move data from one physical disk to another, even if they have different sizes or characteristics.
Q65. What is the maximum length for a file name on Linux?
Ans. 255 bytes is the maximum length for a file name. But if you combine file name and path name, the maximum length is 4096 bytes.
Conclusion
Linux is the most secure operating system. It will never go out of use because of its high efficiency. The Linux interview questions covered in this blog will help you ace your next job interview. When in doubt, you can refer to this article again and get all Linux FAQs answered here.
Top Trending Tech Articles:
Career Opportunities after BTech | Online Python Compiler | What is Coding | Queue Data Structure | Top Programming Language | Trending DevOps Tools | Highest Paid IT Jobs | Most In Demand IT Skills | Networking Interview Questions | Features of Java | Basic Linux Commands | Amazon Interview Questions
FAQs
What is the difference between UNIX and Linux operating systems?
UNIX is a proprietary operating system developed in the 1970s, while Linux is an open-source operating system based on UNIX and released in 1991. Linux has since become one of the most popular operating systems, and is used in a wide range of devices, from servers to smartphones.
Explain the boot process in Linux?
The boot process in Linux involves several steps, including loading the kernel, initializing the system, and starting init processes. The kernel initializes hardware, mounts the root file system, and starts the init process, which is responsible for starting other system services and daemons.
What is the purpose of the /etc/fstab file in Linux?
The /etc/fstab file in Linux is used to specify the file systems that should be mounted at boot time. This file contains information about the file system, including the device name, mount point, file system type, and options for mounting the file system.
How the process of Linux in managed?
Processes in Linux can be managed using various tools, including the top command, which displays real-time information about system processes, and the ps command, which provides information about running processes. The kill command is used to terminate processes, while the nice and renice commands can be used to adjust the priority of processes.
How to configure and manage network interfaces in Linux?
Network interfaces in Linux can be managed using the ifconfig and ip commands. The ifconfig command can be used to view and configure network interfaces, while the ip command provides more advanced network configuration options. Network configurations can also be stored in the /etc/network/interfaces file, which is used to define network interfaces and their configurations at boot time.



![Latest Accenture Interview Questions and Answers [2025]](https://images.shiksha.com/mediadata/images/articles/1736421265php8DOPoT_b.jpeg)