What is a digital signature?
To conduct day-to-day transactions, an increasing number of people and organizations are turning to digital documents rather than paper documents. Why? The main reason - It help save environment and resources. But, how are we achieving this? The answer - digital signature.
With the increasing digitization of documents, the importance of security and authenticity can't be ignored. In the digital world, a digital signature serves the purpose of verifying that the document has not been tampered with. It assures both sender and receiver that the document's content is the same.
Digital Signatures are an important topic in cyber security. If you are intrested in making a career in cyber security? If so, pursue online cyber security courses & certifications or online MCA in cyber security!
In this article, we will go over digital signatures in depth. But, before moving forward, let’s go through the topics that we will be covering in this blog:
- What is a digital signature?
- What are the different types of digital signatures?
- How do you create a digital signature?
- How do digital signatures function?
- What is the difference between a digital signature and an electronic signature?
- Benefits of digital signature
- What is a digital certificate?
- Trust service providers (TSPs)
- Certificate authorities (CAs)
What is a digital signature?
Digital signatures work in the same way that electronic “fingerprints” do, and they use a standard format known as Public Key Infrastructure (PKI). A digital signature verifies the signer’s identity and ensures that the documents sent were not forged or tampered with. As a result, this also contributes to improving cybersecurity.
Best-suited Cyber Security courses for you
Learn Cyber Security with these high-rated online courses
What are the different types of digital signatures?
Digital signature certificates (DSCs) are of three types. These three certificates each have their security level. You can use these for specific categories of professionals and industries.
Simple
It ensures that the information in the document, digital data, or message provided by the owner does not conflict with the information in the well-known database. It is available for both personal and professional use. These types of signatures offer the most basic level of security, and you can use them in environments where data compromise is unlikely. Because it is validated solely on an email ID and username, you cannot use this signature type for legal business documents.
An example of this signature is the email signature that we frequently include at the end of emails and checking the terms and conditions box during the software installation process.
Basic
You can use this type of digital signature for personal and private use. It can include transactions with a high level of risk or fraud. Simple signatures are nearly identical to Basic signatures. The only difference between Simple and Basic signatures is the ability to show changes after the document is signed.
You can frequently use these digital signatures for electronic tax filings, such as income tax returns and goods and services tax (GST) returns.
Advanced
It is also used or distributed to organizations and individuals. This provides high-level data security. Before signing an Advanced signature, a person or organization must present their identity before a certifying authority. You can use these digital signatures in e-auctions, e-tendering, e-ticketing, court filings, and other situations where data is at risk or severe consequences of a security breach.
Let’s go through the differences in a tabular format, for better understanding:
| Benchmark | Simple/Class 1 | Basic/Class 2 | Advanced/Class 3 |
|---|---|---|---|
| Level | Basic | Moderate | Advanced |
| Security | Average | Good | Very high |
| Usage | Tax filings | E-ticketing |

How do you create a digital signature?
You can use digital signature providers to create a digitally signed document quickly. They provide an interface for online document sending and signing, and they collaborate with the appropriate Certificate Authorities to provide trusted digital certificates.
Depending on the Certificate Authority, you have to provide additional information. There may also be restrictions and limitations on who you send documents to for signature and what order you send them.
Some of the top providers that allow you to create free digital signatures are:
- DocuSign
- SignRequest
- signNow
- PandaDoc
- Adobe Acrobat Sign
- OneSpan Sign
- Foxit eSign
- Signeasy
How do digital signatures function?
Providers of digital signature solutions adhere to a specific protocol known as (Public Key Infrastructure) PKI. PKI requires the provider to generate two long numbers known as keys using a mathematical algorithm. One key is public, while the other is private.
When a signer electronically signs a document, the signature generates with the help of the signer’s private key. The signer keeps this key securely. The mathematical algorithm functions as a cipher, generating data that matches the signed document, known as a hash, and encrypting that data. The digital signature is created as a result of the encrypted data. The signature is also accompanied by the time the document was signed. The digital signature is rendered invalid if the document is altered after signing.
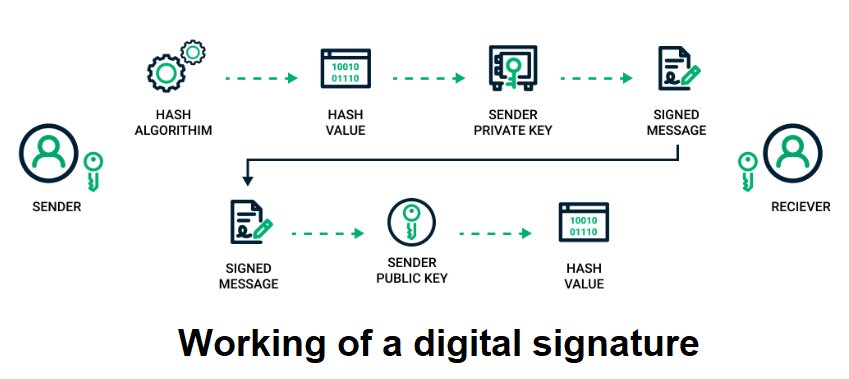
Let’s try to understand the working of a digital signature with the help of a figure and an example.
For example:
Albert uses her private key to sign a contract to sell a timeshare and sends the document to the buyer. The buyer of the document also receives a copy of Albert’s public key. If the public key cannot decrypt the signature, it is not Albert’s signature, or the document has been tempered/ changed since Albert signed it. In that case, the signature is deemed invalid.
Here are the steps to send a digital signature:
- The sender selects the file to be digitally signed in the document platform or application.
- The sender’s computer calculates the unique hash value of the file content.
- This hash value is encrypted with the sender’s private key.
- The original file is sent to the recipient, and it’s a digital signature.
- The receiver uses the associated document application to determine whether or not the file has been digitally signed.
- The receiver’s computer decrypts it using the sender’s public key.
- If the recipient cannot open the document using the signer’s public key, there is an issue with the paper or the sign.
Thus, in this manner, digital signatures are authenticated.
What is the difference between a digital signature and an electronic signature?
Let’s go through the differences in a tabular format:
| Benchmark | Electronic Signature | Digital Signature |
|---|---|---|
| What is it? | It is a legally binding and secure digital form of a wet link signature | It is a secured signature that uses an electronic signature and relies on public key infrastructure. |
| Usage | Verifying a document | Securing a document |
| Vulnerable to tampering | Yes | No, highly secure |
| Verification | Cannot be verified | Can be verified |
| Comprises security features | Less | More |
| Authorization | Not usually authorized | Usually authorized |
| Comes with encryption standards | No | Yes |
| Example | Electronic ticks and scanned signatures | Adobe and Microsoft’s digital signatures |
The fundamental distinction is that a digital signature is used to protect documents and is certified by certification authorities. In contrast, an electronic signature is frequently associated with a contract that the signer agrees to.
Benefits of digital signature
Speed: First and foremost, signing documents digitally is not the paper equivalent in terms of time management and ease of use. Indeed, many signatures from various individuals are required during the sales process. The administrative burden can hinder the sale and, in some cases, force the agreement to be terminated. Using e-signatures in your business could be a difference-maker in terms of cost.
User Experience: Enhancing the user experience is a second underappreciated advantage. The process of printing, signing, and scanning a document to return it is simplified by opening a signing email request. The entire procedure takes under two minutes.
Security: Two aspects of security- Identification and authentication checks provide a high level of protection for document access and signing capabilities.
Fewer errors: By automating the digital signature process, financial implications of human mistakes such as signing mistakes or document loss can be mitigated; errors that slow the process and cause expenses issues if undetected.
What is a digital certificate?
Digital signatures function similarly to electronic “fingerprints.” Digital signatures use a standard format known as Public Key Infrastructure (PKI) to verify the signer’s identity and guarantee that the transmitted documents were not forged or tampered with.
What are trust service providers (TSPs)?
A Trust Service Provider (TSP) is a company that offers a variety of trust services related to the creation, validation, and preservation of e-signatures, e-seals, or digital certificates.
Security is critical to ensure the integrity of certificates used to create electronic signatures. You should store TSPs securely, as many TSPs store signing keys and digital certificates. This ensures the integrity of the TSP’s certificates, e-signatures, and e-seals.
What are certificate authorities (CAs)?
A CA is a reputable organization that issues SSL certificates. These digital certificates are data files that connect an entity to a public key cryptographically. Web browsers use them to authenticate content sent from web servers, ensuring trust in online content. Some examples of certificate authorities include Comodo, GeoTrust, and Symantec.
Conclusion
If you want to learn more about cybersecurity, you can refer to these articles:
Recently completed any professional course/certification from the market? Tell us what liked or disliked in the course for more curated content.
Click here to submit its review with Shiksha Online.
FAQs
Can a single person have two digital signatures?
A document may contain multiple Digital Signatures.
What are three applications for digital signatures?
Digital signatures help achieve three key information security goals: integrity, authentication, and non-repudiation.
Which key is employed in the digital signature?
A public key and a private key are both used.
Can someone forge my digital signature?
Digital signatures are secure, and it isn't easy to forge one.
How does a digital signature ensure document security?
A digital signature encrypts a document with a private key. This ensures that only the intended recipient can access it and confirms the sender's identity and the document's integrity.
Are digital signatures legally recognized?
Yes, digital signatures are legally recognized in many countries. They hold the same legal weight as handwritten signatures as long as they meet specific regulatory requirements and standards.
Do digital signatures work across different platforms?
Yes, digital signatures are compatible across various platforms and software. As long as the necessary encryption standards are followed, they can be verified on different systems and devices.
What happens if a digital signature is compromised?
If a digital signature is compromised, it can lead to unauthorized access or fraudulent activities. Immediate action should be taken to revoke the compromised signature and notify relevant parties.
Is a digital signature the same as an electronic signature?
No, a digital signature uses encryption techniques for security, while an electronic signature is any mark or symbol used to sign a document digitally without encryption.